Hi friends how are you, i hope that you are fine. OK lets move towards today's topic and its about hacking, what is hacking?, a simple answer hacking is "to gain unauthorized access to data in a system, account or computer." a second question how a hacker gain access to a system?, now i tell you the basic way by which a hacker may gain access to a system, computer or account.
There are many ways someone may hack an account, computer or system, and here are the six most usual:
1.Phishing is still the most popular attack vector used for hacking, In a simple phishing attacks a hacker creates a fake log in page which exactly looks like the real web page and then asks the victim to log in. Once the victim log in through the fake page the, the victims "ID" and "Password" is stored in to a text file, and the hacker then downloads the text file and gets his hands on the victims credentials.
2.Keylogging is the easiest way to hack a system. Keylogging sometimes can be so dangerous that even a person with good knowledge of computers can fall for it. A Keylogger is basically a small program which, once is installed on victim's computer, will record every thing victim types on his/her computer. The logs are then send back to the attacker by either FTP or directly to hackers email address.
3.Almost 80% percent people use stored passwords in their browsers to access the web. This is quite convenient, but can sometimes be extremely dangerous. Stealer is a software specially designed to capture the saved passwords stored in the victim's Internet browser.
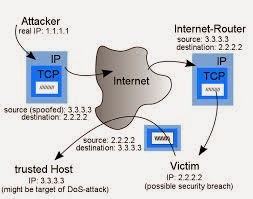
4.If both the victim and attacker are on the same network, an attacker may use a DNS spoofing attack and change the original web page to his own fake page and hence can get access to victims account.
5.Session Hijacking can be often very dangerous if you are accessing web on a HTTP (non secure) connection. In Session Hijacking attack, a hacker steals the victims browser cookie which is used to authenticate the user on a website, and use it to access the victims account. Session hijacking is widely used on LAN, and WiFi connections.
6.Botnets are not commonly used for hacking accounts, because of it's high setup costs. They are used to carry more advanced attacks. A Botnet is basically a collection of compromised computer. The infection process is same as the key logging, however a Botnet gives you additional options for carrying out attacks with the compromised computer. Some of the most popular Botnets include Spyeye and Zeus.
NOTE:
This information is for educational purpose and not to harm others auther is not responsible for any damage.
No comments:
Post a Comment